Table of Contents
Asymmetrical Encryption Using Public/Private Keys
Public key cryptography (asymmetrical cryptography), is any cryptographic system which
uses pairs of keys: public keys which may be distributed widely, and private keys which
are known only to the owner.
The hallmark feature of this methodis the use of asymmetric key algorithms, where the
key used by to perform encryption is not the same as the key used by in decryption.
So, any person can encrypt a message using the receiver's public key. That message
can then only be decrypted with the receiver's private key.
When used for authentication, the host key verifies a holder of the paired private key
by sening a him message encrypted by the owner's public key. Only the holder of the
paired (and secret) private key can decrypt the message (which was encrypted with the
associated public key). Thus who ever is able to send back the decrypted messages
proves that he owns the associated private key.
SSH Asymmetric Encryption Methods
Typically the following asymmetric encryption methods used for public/private key exchange:
Currently (as of 2018), best practise is the use of ED22519 or 4096 bit RSA or keys.
Generating Public/Private Keys
Public/Private key pairs are normally generated using the
ssh-keygen tool or an equivalent function provided by the
ssh client
(e.g. ZOC's built in key generator window).
This will provide the user with a pair of files, e.g. id_rsa and
id_rsa.pub.
The pub file will then be added to the ssh server, while the
private file remains in a folder on the user's computer (under linux this file will
get file system permissions that makes it only accessible by the owner, e.g.
chmod 600 id_rsa).
Uploading the Public-Key to the Server
In order to be used for authentification, the public key part (e.g. id_rsa.pub)
needs to be put in a special file in the user's home folder on the host, so that the ssh-server
can use it to verify the login (in order to to this, you need to login using a different authentication
method, e.g. password).
With ZOC this can be done on a Unix/Linux host using the following sequence of commands:
cd ~/.ssh
rz (or upload the id_dsa.pub file via SCP from ZOC's Transfer-menu)
cat id_dsa.pub >>authorized_keys
ZOC Terminal Download
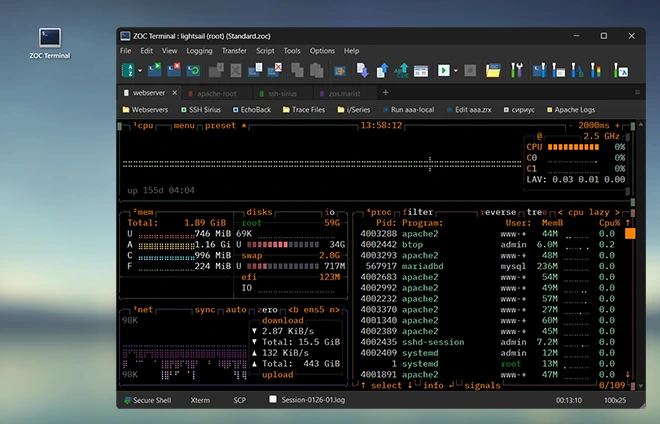
Read more about our ZOC Terminal Emulator,
check its feature list,
look at our screenshots or
start your free 30 days of evaluation today and
download
ZOC Terminal V9.03.2 now.